15-second summary
Getting the full threat intelligence context means manually synthesizing closed-source reports and matching them with your open-source intelligence feeds, a slow, time-consuming process that pulls analysts away from high-value work.
Feedly now lets you directly upload your PDF with its open-source intelligence and use Ask AI to analyze the two together, so you can produce richer, more actionable intelligence without the manual overhead.
In this blog, we’ll show you how to use this feature to save time and improve your analysis with more complete context.
overview
This new capability lets you upload files directly to Feedly and take advantage of powerful features like Ask AI. It provides an intuitive way to analyze your closed-source reports and extract actionable intelligence in seconds.
Since you’re already tracking open-source in Feedly, this feature bridges the gap between your closed and open-source context. The result is richer, more accurate and actionable threat intelligence that accounts for both open- and closed-source domains.
Add open-source reference from the Feedly Threat Graph
Uploading a file means Feedly can analyze your closed-source intelligence using the Threat Graph, a continuously updated knowledge base built from over 10,000 trusted cybersecurity sources.
Threat Graph automatically extracts and correlates key entities from your uploaded files, threat actors, TTPs, malware families, exploited CVEs, and IOCs. When you use Ask AI to analyze a report, you’re not just getting a summary of the document; You’ll also get answers informed by the full open-source intelligence picture.
Feedly does not use your private files to train its AI models, nor share them with third parties. They are used only to strengthen your own analysis.
try it out
Use Case #1: Monitoring threat actor activity
Upload your new incident response report to Feedly and ask the AI to cross-reference each TTP against what’s currently being reported on the open web. This allows you to verify whether the behavior recorded in the report is seen elsewhere.
ready
Based on the uploaded report, which TTPs were used by the threat actor, and are these same techniques being reported in the open web right now? Are other organizations documenting similar behaviors?feedback
Use Case #2: Track Critical Vulnerabilities
If your team receives dense vulnerability reports, Feedly can instantly enrich CVEs with real-time data from the Threat Graph, including exploit status, threat actor activity, and patch availability. This helps you quickly identify which vulnerabilities are being actively exploited, who is using them, and what solutions are available, connecting your internal findings to the broader threat landscape.
ready
Based on the uploaded report, which CVEs were exploited in this incident, are they currently being actively exploited by other threat actors in the open web, and what does the latest reporting say about patch availability and exploit status?feedback
Use Case #3: Identify Cyber Attacks
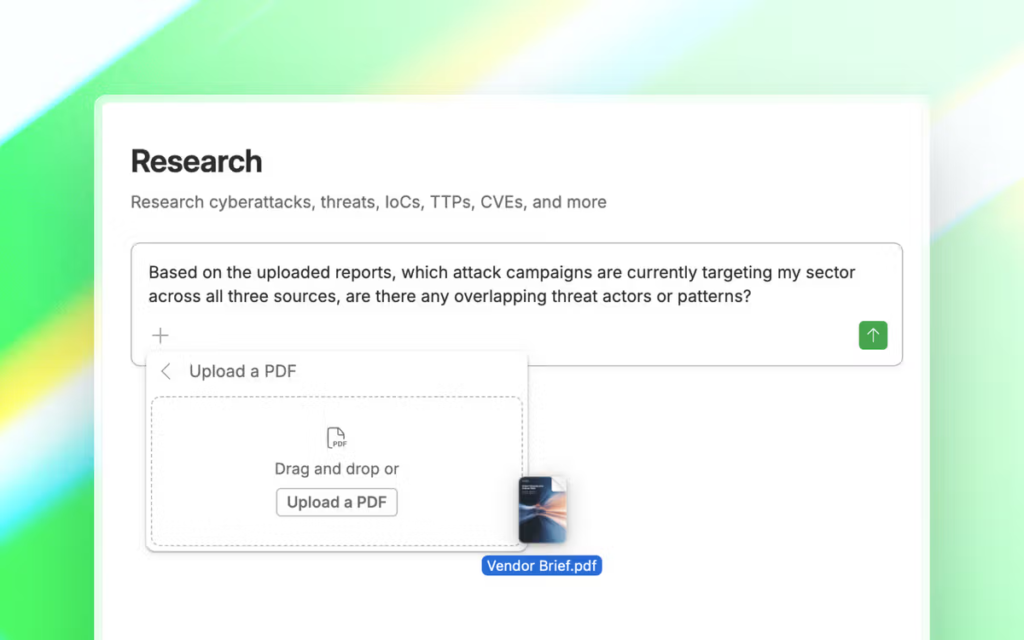
Your ISAC bulletin, a vendor threat brief, and an industry outlook report all arrived this week. Instead of reading each one separately, you can upload all three to Feedly and let Ask AI synthesize them. This will identify overlapping threat actors and recurring attack patterns that should be monitored.
ready
Based on the uploaded reports, which attack campaigns are currently targeting my sector across all three sources, are there any overlapping threat actors or patterns?feedback
Use Case #4: Collect IOC
To check if they appear in active campaigns on the open web, extract IOCs directly from their CERT bulletins and attribute them to threat actors and malware families. This gives you context in real time as to whether those IOCs are still relevant.
ready
Based on the uploaded bulletin, which IOCs are listed, are they currently associated with active campaigns in the open web, and what threat actors and malware families are they attributed to?feedback
conclusion
The four use cases above are just the beginning. Any closed-source reports in your workflow (government advisories, ISAC bulletins, incident response reports, vendor assessments) can be uploaded to Feedly and queried as you require. Ask: Which threat actors are still active in this report? Are these CVEs being exploited in the wild? Has anything changed since this advice was published? Answers can come from your uploaded documents alone, or from both your documents and the open web. You control your workflow and your sources, so you can enrich your threat intelligence and context.
Closed-source and open-source intelligence don’t need to live in different places
Upload your PDF to Feedly and analyze everything in one workflow, no manual bridging required.
start free Trial